Quantum computers are moving from lab curiosity to board-level risk. When a machine reaches a few thousand stable qubits, RSA and ECC crumble. A January 2026 Bain survey of 182 tech leaders found only 12 percent practice quantum-readiness even though 71 percent expect attacks within five years. Regulators concur: NIST’s first three post-quantum standards (August 13, 2024) triggered mandatory crypto inventories, and banks now write PQC milestones into contracts.
Specialist auditors now map keys, model quantum threats, and plan phased upgrades—yet quality varies widely. This guide ranks the seven firms that lead today, explains their strengths and gaps, and helps you start a quantum-safe roadmap before time runs out.
2029 to 2033: the make-or-break transition window
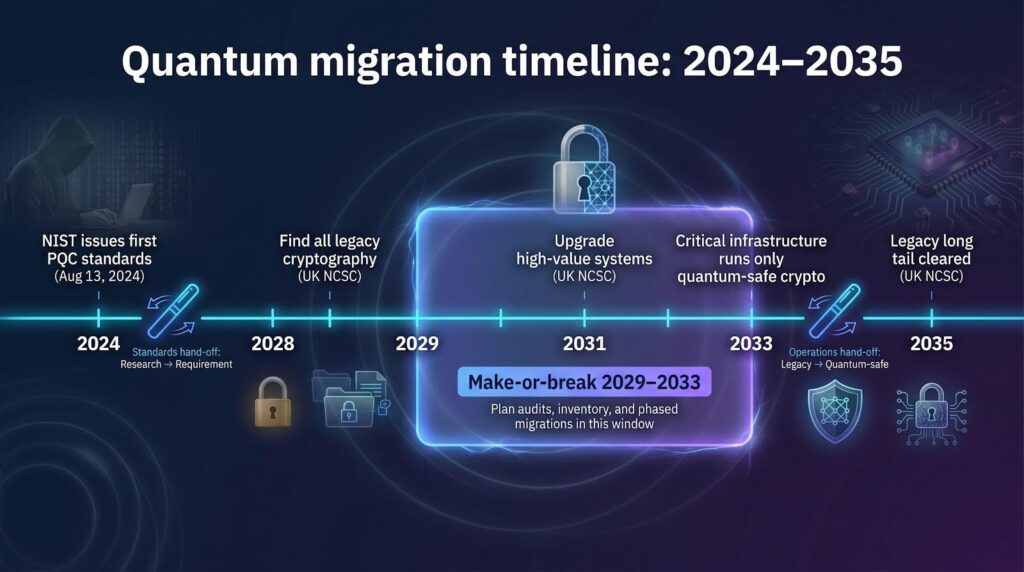
Think of the next seven years as a relay with two hand-offs. NIST fired the starter pistol on August 13, 2024, when it released the first three production-ready post-quantum standards. That moment turned research into a requirement for every industry that guards long-lived secrets.
The second hand-off lands no later than 2033, when agencies and critical infrastructure must run only quantum-safe algorithms. The UK National Cyber Security Centre already instructs organizations to find all legacy cryptography by 2028, upgrade high-value systems by 2031, and clear the long tail by 2035. Boards see the same countdown, and investors treat quantum risk like climate disclosures: material and deadline-driven.
Between those dates lies a messy middle. Hardware gains at IBM, Google, and many startups are shrinking the qubit gap faster than experts predicted. Attackers follow a “steal now, decrypt later” playbook, collecting encrypted data today for future reading. If your information must stay confidential for decades, waiting until 2030 is choosing to lose.
That urgency is why readiness audits matter now. They give you a complete inventory, a risk-based schedule, and, crucially, the breathing room to migrate in phases instead of scrambling later. Nail the roadmap in this window and quantum computing is just another wave you ride past; miss it and the wave crashes through your security stack.
How we picked and scored the seven leaders
Ranking security partners is useful only when the yardstick is solid.
We began with one filter: the firm must run live, fee-based post-quantum readiness audits today. Pure product vendors, think-tank labs, or consultancies still “exploring the opportunity” never made the long list.
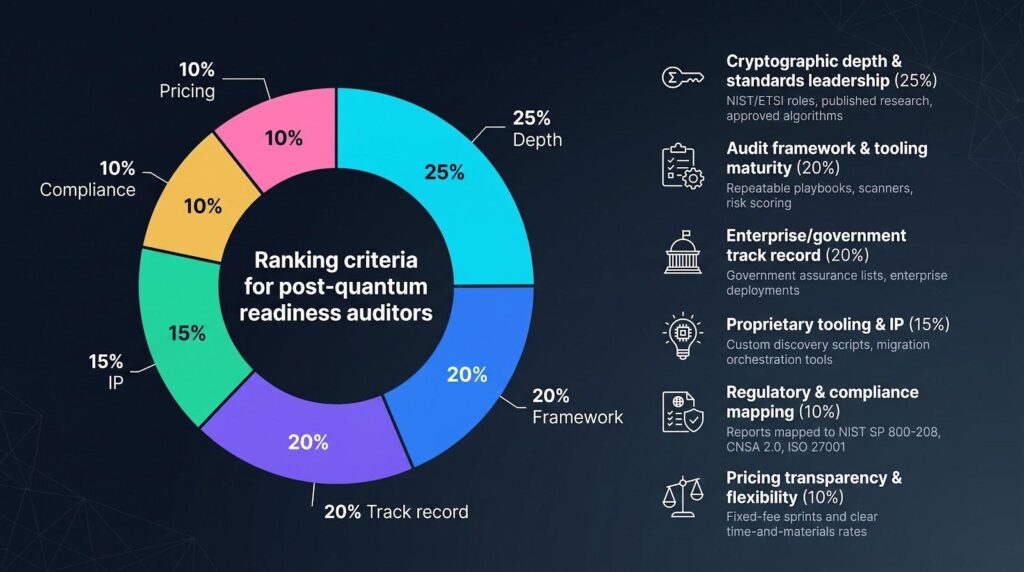
From there we rated each candidate against six weighted factors tied to real buying pain:
- Cryptographic depth and standards leadership (25 percent)
We looked for staff who publish papers, sit on NIST or ETSI working groups, or write code now included in approved algorithms. Vendors that only resell third-party tools scored low. - Audit framework and tooling maturity (20 percent)
Does the firm bring repeatable playbooks, automated scanners, and clear risk scoring? Or is the engagement just a slide deck? Only the first group earned top marks. - Verified enterprise or government track record (20 percent)
We checked press releases, case studies, and government assurance lists. The UK National Cyber Security Centre, for example, has publicly “assured” only eight global consultancies for PQC overhauls. Firms on that list gained credibility. - Proprietary tooling or intellectual property (15 percent)
Custom discovery scripts, migration orchestration platforms, and hybrid-certificate generators all cut time and cost for you. - Regulatory and compliance mapping (10 percent)
We favored teams that align findings to frameworks such as NIST SP 800-208, NSA CNSA 2.0, or ISO 27001 so the report drops straight into an external assessment. - Pricing transparency and flexibility (10 percent)
Fixed-fee readiness sprints and clear time-and-materials rates outperform “contact sales” vagueness.
Scores across these pillars rolled into a one-to-five composite that sets the ranking order in the vendor profiles.
Why just seven firms? Very few meet every inclusion hurdle with public proof. That scarcity matters. Demand is rising, regulators are tightening deadlines, and 91 percent of organizations still lack a formal post-quantum roadmap. Wait until 2028 and you may find every top auditor already booked.
1. Deloitte: the enterprise Swiss Army knife for quantum risk
If your mandate spans thousands of applications, multiple regions, and strict regulators, Deloitte is often the first number you dial.

Deloitte Quantum Cyber Readiness Services Webpage Screenshot
Its Quantum Cyber Readiness program feels less like a consulting engagement and more like a military operation. Teams of cryptographers, cloud architects, and compliance lawyers arrive with scanners that surface every RSA and ECC remnant. They then map each finding to NIST, ISO 27001, or CNSA 2.0 controls. You leave with a living cryptographic bill of materials, risk-ranked remediation sprints, and board-ready metrics that track progress each quarter.
Scale is Deloitte’s core asset. The firm advises governments that are shaping national PQC roadmaps and brings a global team of specialists to manage complex, multi-year transitions. That depth matters when auditors or shareholders ask, “Why did we trust this playbook?”
You also get subject expertise. Deloitte staff chair standards meetings, publish research, and co-wrote a quantum-readiness playbook with the World Economic Forum. When regulators adjust guidance, your Deloitte lead likely heard the change in the meeting where it was drafted.
The trade-off is cost. Engagements often start with a fixed-fee discovery sprint but quickly grow into multi-year transformations. Mid-market firms sometimes balk at the price tag or the staffing footprint. If you want a light-touch assessment, keep scrolling. If you need a global quarterback to drive policy, architecture, and execution in sync, Deloitte tops the list.
2. IBM Consulting: turning lab-level R&D into practical migration playbooks
IBM designs quantum computers and helps you defend against them. That twin role gives its Quantum-Safe Transformation Services an inside view of where threats are headed and which countermeasures scale in production.
IBM Quantum-Safe Transformation Services Webpage Screenshot
Projects start with Discover, which auto-maps every certificate, key store, and encrypted data flow across on-prem, mainframe, and multicloud estates. The output is a cryptographic bill of materials with severity tags that mark “fix first” assets. Next, the Observe phase runs simulated quantum attacks to show executives which processes would fail first. The final Transform phase folds remediation into existing pipelines, swapping in hybrid or fully post-quantum algorithms and validating performance on IBM’s test harnesses.
Clients like the time savings: proprietary scanners cut weeks from inventory, and the team can tap IBM Research for algorithm tweaks when edge cases arise. Banks also value that IBM zSystems and Cloud services already support Kyber and Dilithium hybrids, so proofs of concept run on equipment many firms own today.
There are caveats. IBM solutions often bundle the company’s hardware or cloud stack. If you are committed to Azure or AWS, confirm tool compatibility early. Pricing sits lower than a big-four consultancy but higher than boutique advisors, roughly mid-six figures for a global assessment and pilot.
Bottom line: when you need deep technical execution and confidence that recommendations align with NIST’s evolving standards, IBM blends hardware expertise and consulting polish in one shop.
3. Entrust: PKI veterans making crypto-agility real
When your business depends on certificates, Hardware Security Modules, and identity services, Entrust feels like home ground. The company has issued digital credentials since the dial-up era, so its move to post-quantum security was an upgrade, not a reinvention.
The centerpiece is the Cryptographic Center of Excellence, a consulting arm that pairs advisory workshops with hands-on tools. First, the team runs a readiness assessment that sweeps your PKI hierarchy, code-signing flows, and data-at-rest controls. You receive a “cryptographic debt” ledger that highlights expired algorithms and hard-coded keys. Next comes prototyping. Clients can spin up hybrid X.509 certificates in Entrust’s cloud PKI or load a PQC option pack onto nShield HSMs to test Kyber and Dilithium in production-like traffic.
Most enterprises cannot rip out PKI; they must evolve it. Entrust lets you trial quantum-safe algorithms alongside RSA, proving performance and interoperability before you flip the switch.
Regulators value that rigor. Entrust engineers sit on the NIST and IETF working groups that write the standards you must follow, and its cloud PKI issued the first commercial post-quantum certificates in 2024. That early work means documented playbooks rather than experiments.
Mind the scope, though. Entrust excels at trust infrastructure; broader application discovery or zero-trust strategy will need partner firms. Pricing starts with a fixed-fee workshop and moves to consumption-based licenses for toolkits and cloud certificates.
If your main risk is “our certificate chain breaks on Q-Day,” Entrust offers a pragmatic, test-before-commit path to crypto-agility.
4. Project 11: crypto-native specialists guarding digital assets before Q-Day
Banks and exchanges hold billions in blockchain value that sits one private-key breach away from disaster. Project 11 aims to close that gap. Founded by lattice-cryptography PhDs and former U.S. Army Special Operations officers, the New York startup zeroes in on making Bitcoin, Ethereum, and private ledgers quantum-resistant long before large-scale qubits arrive.
Project Eleven Quantum-Safe Blockchain Security Homepage Screenshot
The flagship Yellowpages platform builds post-quantum wallets and transaction flows that fit existing custodial systems. No forklift upgrade, no chain fork. During an audit, Project 11 inventories every signing process, cold-storage vault, and API endpoint that touches a key. The team then deploys Yellowpages hybrids—Kyber for key exchange, Dilithium for signatures—so you can run parallel transactions on testnet and mainnet without risking funds.
Proof, not promises, sets Project 11 apart. The company’s Project 11 Q-Day Prize offers one Bitcoin to anyone who can crack an elliptic-curve target on real quantum hardware; in April 2026 a researcher earned the reward by breaking a 15-bit key, the largest public quantum attack on elliptic-curve cryptography to date. That bounty pressure-tests their threat model while showing confidence in their math. Investors noticed, leading a twenty-million-dollar Series A in January 2026 earmarked for audit capacity.
The narrow scope is both asset and limit. If your threat model covers cross-border payments, stablecoins, or tokenized assets, Project 11 speaks your language. If you need an enterprise-wide inventory across HR systems and SCADA networks, pair them with a broader integrator.
Pricing starts near one-hundred-fifty-thousand dollars for a scoped digital-asset readiness audit, with Yellowpages licenses scaling by wallet volume. For crypto-heavy firms that cannot risk a single compromised key, that is affordable insurance against a costly future.
5. Post-Quantum: battle-tested products for government-grade communications
Post-Quantum is the elder statesman of this list. Founded in London in 2009, the company built quantum-safe VPNs and secure messaging long before most CIOs noticed the topic. That head start shows in customer proof: its PQ VPN wrapped a live NATO network in 2022 and has passed interoperability tests across varied environments.
An engagement begins with the usual cryptographic discovery, yet the real differentiator comes next. Instead of handing you a slide deck, Post-Quantum installs its own VPN, PKI, or secure email stack beside legacy systems. Your team can route traffic through lattice-based tunnels in real time, measure latency, and test failover. Seeing post-quantum packets cross production gear turns theory into muscle memory quickly.
The firm’s history in defense and telecom means consultants speak the language of classified enclaves, wireline protocols, and carrier-grade uptime. They also contributed Classic McEliece, a finalist in the NIST competition, so algorithm expertise is in-house, not borrowed.
Where they fit best: organizations with mission-critical communications that cannot afford downtime during a crypto cutover. The trade-off is process transparency. Post-Quantum focuses on delivering a working solution, so methodology documents can feel sparse compared with big-four rigor. If you need detailed Gantt charts for every milestone, negotiate deliverables early.
Pricing is project-based and aligns with appliance rollouts, often six figures for a pilot covering multiple sites. For CISOs who lose sleep over interceptable links, Post-Quantum offers a proven, plug-and-play safety net.
6. QuSecure: drop-in orchestration for quick wins on the network edge
Some organizations cannot wait months for code refactors. They need a fast way to cloak data in transit before the next compliance audit. That is QuSecure’s strength.
QuSecure QuProtect Hybrid TLS Gateway Product Page Screenshot
The California startup ships QuProtect, a software gateway that negotiates hybrid TLS sessions automatically. Install the gateway on-prem or in a cloud VPC, route traffic through it, and your VPNs, SD-WAN links, and web services speak Kyber alongside RSA. No hardware swap or kernel patch.
During an engagement, the QuSecure team begins with a network assessment that pinpoints choke points such as satellite uplinks, B2B APIs, and remote sites where quantum-vulnerable keys protect valuable data. They capture packets, measure exposure, and stage QuProtect pilots in hours, not weeks. That speed earned the company a U.S. Space Force satellite link contract in 2023, a live demo that still resonates in defense circles.
QuSecure balances its youth with alliances. Accenture resells the platform, and Deloitte lists it among preferred tools for rapid crypto-agility sprints. Algorithms live at the protocol layer, not in proprietary hardware, so you avoid vendor lock-in while still getting enterprise support.
There are limits. QuProtect focuses on traffic encryption and stops at the application boundary. If you also need database, file, or code-signing remediation, budget a second workstream. Pricing follows a SaaS model, with costs tied to protected throughput, keeping expenses predictable as coverage grows.
For security leaders facing a 90-day audit deadline, QuSecure provides the fastest path to show measurable progress.
7. Encryption Consulting: boutique precision for policy-heavy environments
Big integrators can feel like cruise ships. Encryption Consulting is a speedboat. The Texas firm focuses solely on cryptography, so every consultant you meet can shift between PKI architecture, code reviews, and audit-support language without calling another practice.
Engagements begin with a Quantum Threat Assessment that inspects source code, CI/CD pipelines, and vendor SDKs—spots general security scans often miss. Findings flow into a Quantum Readiness Roadmap aligned line by line with NIST SP 800-208 and NSA CNSA 2.0. For compliance-driven sectors such as insurance or energy, that clear mapping shortens internal approval cycles.
Clients like the “no PowerPoint only” approach. Encryption Consulting will test post-quantum libraries on your dev branch, benchmark performance, and run tabletop exercises with auditors. Dashboards then track cryptographic inventories over time, keeping the audit current after consultants leave.
Capacity is the limit. The firm can field several squads, but not large armies. Some multinationals pair Encryption Consulting’s deep dive with a global systems integrator for rollout. Pricing stays transparent: fixed fee for the assessment, then time and materials for remediation support.
If your board demands a clear audit trail and you want cryptography specialists guiding each step, Encryption Consulting provides boutique rigor without enterprise bloat.
Comparison snapshot: which audit partner fits your puzzle?
We have covered a lot of ground, so let us zoom out and line the seven contenders side by side. The matrix below distills the attributes most buyers ask about first: scope, primary strength, and what to watch for.
| Vendor | Core focus | Notable strength | Geographic reach | Engagement style | Primary caveat |
| Deloitte | End-to-end enterprise transformation | Global bench depth and World Economic Forum partnership | 150+ countries | Multi-year program | Premium cost and footprint |
| IBM Consulting | Tool-driven discovery plus migration | Hardware and standards insight in one shop | Global | Phased playbook | Bundles often favor IBM stack |
| Entrust | PKI and certificate agility | First commercial PQ-ready PKI as a service | Global | Workshop plus product license | Narrower focus on trust infrastructure |
| Project 11 | Blockchain and digital assets | Yellowpages post-quantum wallets | North America, EU | Fixed-scope crypto audit | Limited reach outside crypto stack |
| Post-Quantum | Secure communications and VPN | A decade of real-world deployments | UK-led, EU/US projects | Pilot then rollout | Fewer process documents than big four |
| QuSecure | Network-layer overlay | QuProtect rapid hybrid TLS | North America, EU, APAC partners | SaaS throughput model | Stops at the application boundary |
| Encryption Consulting | Standards-heavy advisory | Deep policy mapping and proofs of concept | North America, selective global | Fixed fee plus time and materials | Limited delivery scale |
Use the table to focus your search. If certificate sprawl worries you, Entrust stands out. Racing a ninety-day network audit? QuSecure is likely the front-runner. Need credibility with regulators? Deloitte or IBM provide that confidence.
Remember, any of these firms can succeed when their strengths match your most pressing risk. Let the matrix guide your matchmaking conversation.
Picking your partner: a practical decision checklist
Choosing a post-quantum auditor is not like buying an antivirus license. The engagement rewires core security plumbing, touches several business units, and sits under regulatory scrutiny. Use the questions below with every vendor on your shortlist.
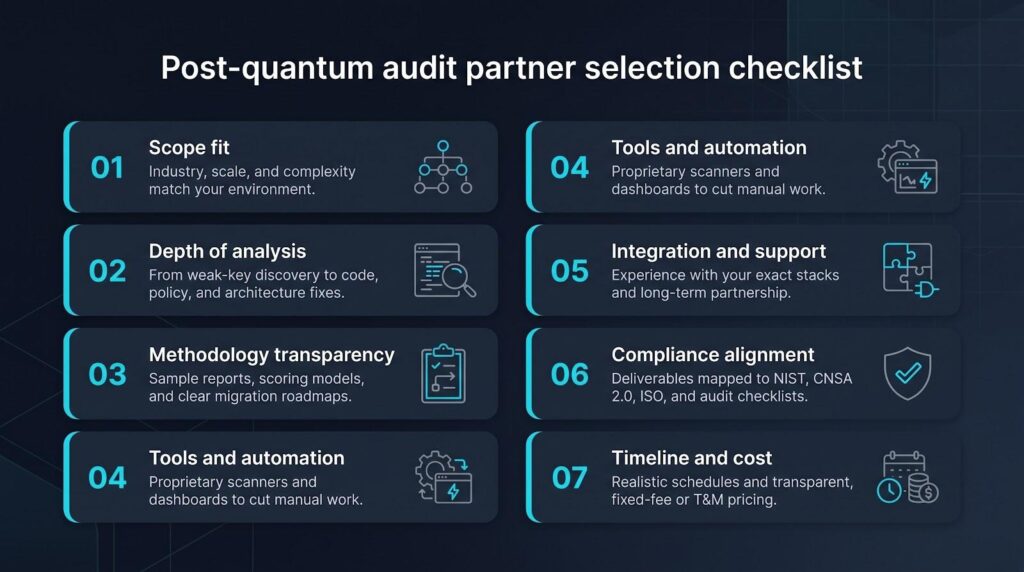
- Scope fit – Ask, “Have you audited systems in our industry and of our size?” A bank with twenty-five million certificates needs a different playbook than a SaaS firm with three microservices.
- Depth of analysis – Will the team just flag weak keys, or also help remediate code and policies? Firms such as Entrust or IBM stay through execution; some boutiques hand you the to-do list and leave.
- Methodology transparency – Request a sample report. Look for clear scoring of crypto assets, references to NIST SP 800-208, and an explicit migration roadmap.
- Tools and automation – Proprietary scanners from IBM or QuSecure can inventory thousands of endpoints overnight, saving weeks of manual work.
- Integration and support – If you plan to test Kyber in AWS Lambda, confirm the auditor has tried that exact stack, not just theory.
- Compliance alignment – Regulated sectors should insist on deliverables that map findings to auditors’ checklists. Encryption Consulting excels here.
- Timeline and cost – A focused readiness sprint usually takes four to eight weeks. A full migration roadmap can run months. Get fixed-fee quotes where possible and make sure they include post-engagement Q&A.
Treat these questions as non-negotiable. The right vendor will answer each one with concrete examples, not marketing gloss. When that happens, you know you have a partner who can steer you safely across the quantum divide.
Trends shaping tomorrow’s audits: stay ahead of the curve
The vendor you hire today must adapt to forces already reshaping quantum-safety.
- Hybrid cryptography is moving from lab demo to deployment default. Most readiness reports now recommend running post-quantum algorithms with RSA or ECC, keeping backward compatibility while new standards mature.
- Automation and crypto-agility will replace one-off fixes. Leading auditors package dashboards and CI/CD hooks that flag risky code the moment you push a commit, shifting the goal from “migrate once” to “swap algorithms whenever standards change.”
- Supply-chain scrutiny is rising. Regulators know your encryption is only as strong as every npm, Maven, or container dependency, so forward-looking firms already scan third-party libraries during the audit.
- Regulatory pressure keeps climbing. The EU NIS2 directive and U.S. federal memos now call for cryptographic inventories by name. By 2027, auditors may ask for proof that every key and certificate has a quantum-safe roadmap.
- Hardware progress keeps accelerating. Updated roadmaps from IBM and Google shave months off earlier qubit targets, pushing boards to fund audits sooner rather than later.
Conclusion
The 2029-to-2033 transition window is short, and the right audit partner depends on which risk keeps you up at night. Deloitte and IBM bring global enterprise muscle, Entrust and Post-Quantum harden trust infrastructure and communications, Project 11 protects digital assets, QuSecure delivers rapid network-edge wins, and Encryption Consulting offers boutique policy depth. Track the hybrid-crypto, automation, supply-chain, and regulatory currents above. Pick the firm whose strengths match your most pressing exposure, kick off a scoped readiness sprint now, and you will reach 2033 with a quantum-safe stack instead of a scramble.